Black Hat 2016: What we learned at the conference
At the annual Black Hat USA 2016 cybersecurity conference, held August 1-4 in Las Vegas, researchers and companies from around the world gathered to assess the latest threat environment and discuss solutions.
The consensus opinion is that the bad guys are still far ahead, but there is renewed hope that by raising awareness of the security flaws that exist in the online world and sharing information about new threats, the risk of identity theft can at least become better managed and hopefully reduced.
As Jeff Moss, the conference founder and security expert, told Black Hat attendees in his keynote remarks, “We’ve got the most eyeballs on us this year than ever before. We can really screw it up or we can become trusted.”
There was one message that came through loud and clear at this year’s conference: protecting individual users and companies from data theft will be more challenging than ever before.
The crux of the problem, as described quite succinctly during the conference by Dan Kaminsky, is that the engine of the Internet now driving the exchange of massive amounts of data and billions of dollars in sales revenue was never intended to be a highly secure technology tool.
“The Internet is not designed for security, it’s designed for moving pictures of cats,” said Kaminsky, an internationally respected technologist who is one of the seven “shareholders” in the world who holds the keys capable of restoring the domain name system if necessary.
 In the course of three full days of briefing sessions, a number of highly-respected security researchers presented findings that clearly highlighted the difficulties which lie ahead. One example of this could be found in EMV chip cards which were finally introduced into the U.S. consumer market over the course of the past year.
In the course of three full days of briefing sessions, a number of highly-respected security researchers presented findings that clearly highlighted the difficulties which lie ahead. One example of this could be found in EMV chip cards which were finally introduced into the U.S. consumer market over the course of the past year.
These chip-embedded cards were designed to make payment processing and financial transactions more secure than the previous “magnetic stripe” cards. While not all merchants have adapted their point-of-sale terminals to accept the chip cards, most American consumers have been issued at least one debit or credit card that contains the new technology.
At Black Hat, two different groups of security researchers presented evidence which showed major security flaws in the chip card’s ability to protect private financial information. Researchers from Rapid 7, an IT security and analytics company, showed how they could compromise the chip card by inserting a “shimmer” into the card slot of an ATM terminal.
This thin device, which sits between the card and the machine reader, modulates electrical impulses from the embedded card chip. By essentially “hacking” into the chip itself, the researchers were able to take full control of the ATM and loot a user’s bank account.
Similar research conducted by a team from NCR also used a “shimmer” to hack a point-of-sale payment terminal. But in this case, they were able to obtain a credit card holder’s “CVV” secret code and their pin.
This compromise was pulled off by taking control of the payment terminal and injecting a fake screen where an unsuspecting customer would be asked to enter their CVV and pin codes to complete a transaction. Using Internet connectivity, the bad guys would capture and store this information and then have financial control over a customer’s debit or credit account.
“Essentially, we had a full compromise of the pin pad data,” said security researcher Nir Valtman of NCR.
Presentations at this year’s conference also highlighted rising vulnerability in the mobile platform as well. Increasing reliance on smartphones as the key communications tool in our daily lives has made these a prime target for criminals seeking to obtain private information.
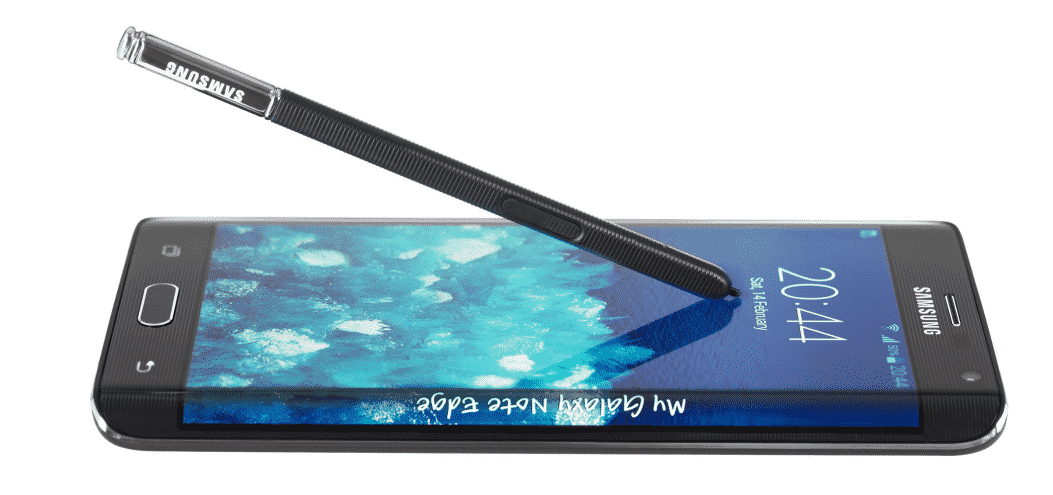 Security researchers from Atredis Partners described how flaws in the Android platform are currently being exploited. While Android smartphones in the U.S. still remain relatively secure, there has been a significant rise in exploitation of these devices in other countries around the world according to the Atredis findings.
Security researchers from Atredis Partners described how flaws in the Android platform are currently being exploited. While Android smartphones in the U.S. still remain relatively secure, there has been a significant rise in exploitation of these devices in other countries around the world according to the Atredis findings.
The researchers found that criminal hackers are exploiting vulnerabilities in the smartphone’s chip processor. Whereas Apple’s iOS platform is given regular updates, the Android platform is fragmented and difficult to keep up-to-date. This makes it harder for the phone’s security tools – TrustZone and BootLoader – to handle hardware bugs which are often downloaded through malicious apps.
Even commonly used online services, such as Airbnb, are not immune to the risk of identity theft. Jeremy Galloway of Atlassian delivered a presentation where he documented the potential for a malicious guest to intentionally gain control of personally identifying information by installing malware on a consumer-grade home router. Criminals could then gather data on the homeowner or future guests too.
To minimize the risk, Galloway recommended that Airbnb guests use their own private hotspots rather than connect to a home network, and that homeowners who rent their places out take a simple step to control access to the router by placing it in a locked cabinet. In response to Galloway’s presentation at Black Hat, Airbnb recently issued a statement that they routinely advise homeowners to change their router password after every guest to further reduce the hacking risk.
The Black Hat gathering is also an opportunity for companies in the cybersecurity space to showcase new technologies specifically designed to deal with the threats that researchers uncover. This year’s event showed that there is a growing business where companies have built extensive technology around not just identity theft protection, but also identification and recovery of sensitive data.
One such firm present at Black Hat this year – SecurityScorecard – previewed what they are calling the “world’s first security search engine.” Their proprietary, cloud-based platform called “ThreatMarket” is designed to be a comprehensive look at threat vectors around the world. This includes researching IP addresses, leaked personally identifying information, improper server setups, and more.
Another company, 4iQ, uses a Google-like crawler to find and index all personal identifying information. They can track lost or leaked documents not just in the mainstream Web, but the deep and dark Web where contents are not indexed by traditional search tools.
One key trend in the cybersecurity world is the development of new protection software that companies can use internally to protect sensitive personal data of their employees. Often, hackers who can’t gain access to valuable proprietary company secrets will capture identifying material such as bank account numbers (for direct deposit) and social security numbers in an effort to build a database of identities.
Spirion (formerly IdentityFinder), who just announced a new partnership with the Patelco Credit Union, identifies weak links in an organization’s data structure and then implements protections of sensitive personal information such as medical records, credit card numbers and other highly personal employee files.
Buguroo, a spin-off from Deloitte’s European cyberthreat center, follows a similar path in providing new technologies to businesses seeking to protect their employee records. Buguroo’s tools detect malware threats inside the company network and identify Web brand identity fraud, often through infected mobile devices or danger zones like hotel hotspots.
A growing point of vulnerability in the security world involves the explosion of IoT (Internet of Things) devices. With so many consumer products (fitness trackers, cars, home thermostats) becoming Internet connected, the risk of criminals obtaining personal information has risen as well.
At the Black Hat gathering, security experts demonstrated how they could remotely take control of the brakes and steering of a Jeep Cherokee at highway speeds. Another team, showed how they could easily hack into the Philips Hue, an Internet-connected light bulb.
Companies like Arxan are focusing on the vulnerability in IoT devices and developing software tools to uncover and defend against such attacks. Arxan recently announced that they are now protecting over 500 million devices globally and saw record-breaking corporate growth in the first half of 2016.
Many security industry analysts believe that the next wave of cyberdefense tools to combat identity theft will have to come from protecting Internet connected consumer products.
 A lot of smartphone users may not be fully aware of it, but every device carries a microphone in addition to the camera. Both the photo/video and microphone capability of the smartphone can be activated surreptitiously through a malware infection and used to collect a treasure trove of personal data.
A lot of smartphone users may not be fully aware of it, but every device carries a microphone in addition to the camera. Both the photo/video and microphone capability of the smartphone can be activated surreptitiously through a malware infection and used to collect a treasure trove of personal data.
At Black Hat, a company called Privoro demonstrated one product designed to protect smartphone users from location tracking as well as audio and video eavesdropping. A plastic case equipped with blocking sensors covers the phone and then audio, video or GPS functions can be enabled to disabled simply by pushing a section of the case up or down and activating a built-in switch.
Privoro was started three years ago and emerged from stealth mode last January when they unveiled their technology at the Consumer Electronics Show (CES). They are also developing a similar product for laptop computers which have video and audio capabilities as well.
Despite the work of security researchers to uncover new flaws and companies to develop sophisticated tools to safeguard the privacy of information, the burden of protection still falls on the individual. This was a common theme throughout the Black Hat conference this year and it was echoed in a number of the presentations.
One example of this can be found in the work of Zinaida Benenson, a researcher at the University of Erlangen-Nuremberg. She presented the results of a study where spear phishing messages from non-existent people were sent to participants using both Facebook and standard email. The results showed that a subtle manipulation of the social nature of the message (“here’s some pics from last night’s New Year’s Eve party!”) led more people to click an enclosed unsafe link when the communication was delivered through Facebook rather than standard email.
Identity theft continues to grow because of human nature and continued unsafe practices like clicking on unknown links in suspicious messages. As the Black Hat conference made clear, unless users become better educated in how to guard against attacks, the party will indeed be over.

